Announcement: Upcoming changes to the permission grant flow for OAuth apps

This announcement is intended for app developers who use the Zoho API console.
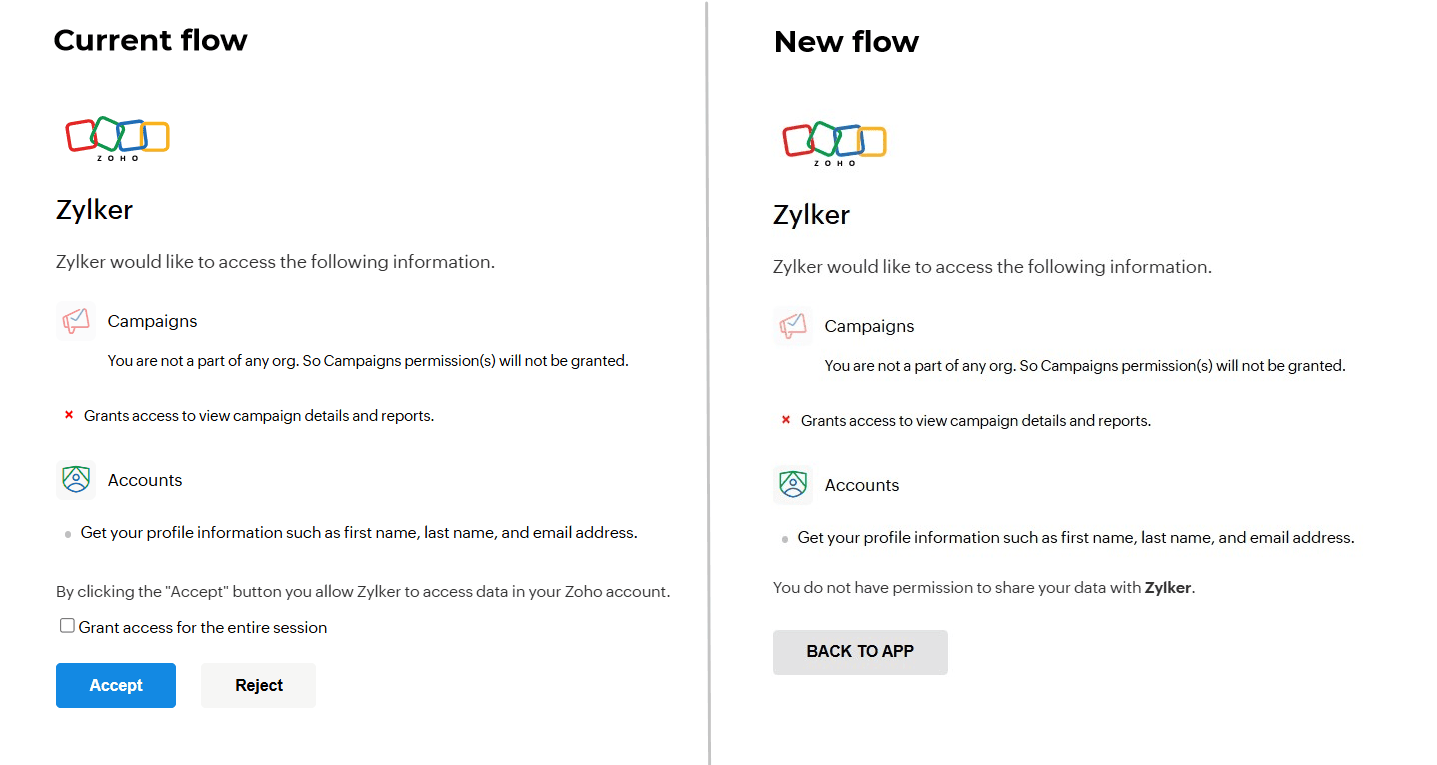
We're going to implement an important update to the way users grant permission for the OAuth apps created through the API console.
What’s changing?
Currently, users can grant access to your app even if they do not have an account in any of the Zoho apps included in the requested OAuth scopes. Starting February 10, 2025, this will no longer be allowed when certain apps are included in the request. These apps include the below:
|
- Bigin
|
- PhoneBridge
|
|
- Campaigns
|
- QEngine
|
|
- CRM
|
- Recruit
|
|
- Desk
|
- Solution
|
|
- IOT
|
- ZeptoMail
|
|
- Marketing Automation
|
|
From the effective date, when scopes of any of the above apps are included in a request:
- Users must have an account in the specified Zoho apps requested by your OAuth app to grant access to the required permissions.
- If a user doesn't have an account in even one of the Zoho apps mentioned, they will be unable to grant permission.
- The "Accept/Reject" buttons will be replaced with the "Back to app" button. When users click this, "error=no_org" will be sent as response to your app's redirect URL.
Why this change?
This change is to make sure the users don't encounter any issues with the apps they've granted access to. If there is no resource to access, the app will not work properly even if the user has granted the necessary permission. This results in poor user-experience.
Also, when an OAuth app requests specific permissions, it indicates those scopes are essential for the app to function. If any scope is not relevant for the app, those permissions shouldn't be requested to the user.
Recommended actions for app developers
The existing refresh tokens generated for such cases will continue to work. But if the user revokes the permission, they won't be able to grant access to the app again (if they still don't have accounts in the required Zoho apps).
Hence, make sure to audit your apps to ensure they only request scopes that are essential. And, update your app to handle the scenario where authorization fails due to users not having required accounts.
If you have any questions or need support regarding this change, please reach out to us at support@zohoaccounts.com.